23 April 2026
1069
12 min
5.00
Up to +23% Additional Revenue from the "Abandoned Browse" Trigger on Anonymous Traffic: PUMA Case Study
On average, 92–98% of ecommerce site visitors are anonymous. They browse products, compare prices, return multiple times — but never log in or leave a contact.
Every one of those visitors already costs the business an acquisition budget. Some of them will never convert. At least, that's how it looks on the surface. But you already know something about them — provided your analytics and tracking are set up correctly: which page they landed on, which ad brought them, which categories they browsed, which products they opened, what they clicked on, and how long they spent on the site.
Strategy then points in one direction — bring the user back. Retargeting campaigns go live. Ideally, the business runs dynamic ads showing the exact products the visitor viewed. But time passes, the campaign ends, and from that point, they see generic promo offers.
If something catches their interest again, they'll return. They might leave an email or phone number to get a discount or access a special offer.
And that's precisely the moment when most marketing systems start the conversation from scratch. Everything that happened before — previous browse sessions, clicks — is either not stored at all, or not used for personalization.
In practice, the business treats every contact as a first introduction, even when it's not the first touchpoint.
That raises a strategic question:
What percentage of today's revenue exists only because the system remembered the user before they left their contact details?
If the answer is "we don't know" — that's where the largest growth potential lies. Below, we'll show exactly how anonymous behavioral history translates into measurable revenue, and how much a business can realistically earn from it.
What Happens Without a Link to Anonymous History
The typical scenario looks like this:
- A user visits the site anonymously.
- Browses several products.
- Leaves the site.
- Returns via an ad.
- Leaves an email or phone number.
- Receives a standard welcome email (at best, with some selection of the week's promo offers or default categories).
From the system's perspective — this is a "new contact with no history." From the user's perspective — this is already their second or third interaction with the store.
Marketing technically worked. But the intent that had already formed before identification is lost — and as a result:
- personalization is absent and delayed, since it only kicks in at later stages;
- triggers don't hit at the very first moment of intent;
- part of the potential revenue simply goes unrealized.
The Alternative Scenario: When Anonymous Behavior Is Monetized
Now the same user, but with web tracking and history matching (stitching).
Matching
the process of linking anonymous behavior to contact data at the moment of identification.
Web tracking
the technology for collecting and recording user behavioral data on a site: page views, clicks, events, add-to-cart actions, session duration, and other interactions.
The new user journey:
- Visits the site anonymously.
- The system records browsing activity via cookies/device ID.
- The user leaves.
- Returns via an ad or social media.
- Leaves an email or phone number in a discount pop-up or gamified widget.
- At the moment of identification, the anonymous profile and all collected data are matched to the new contact.
- The "Abandoned Browse" trigger fires.
- The user receives a personalized selection of products they viewed earlier, while anonymous — plus a discount.
- A purchase happens within the first few hours.
The key point: personalization works not after the fact, but immediately at the moment a contact appears.
Where most businesses start over from scratch — treating a newly registered user as someone brand new — you gain a competitive edge.
How the System "Remembers" an Anonymous User
While a user hasn't left contact details, the system still records their behavior:
- product/category views;
- events (add to cart, scroll, clicks);
- sessions;
- content interactions.
This data is tied not to an email or phone number, but to anonymous user identifiers — specifically, browser cookies or device ID.
Each browser and device builds a separate history. Until the system receives contact details, these are treated as different, unconnected users.
The anonymous history is stitched to a contact at the moment the system receives any stable user identifier.
This can happen in several ways:
- Click from an email or message. The link passes a contactID (via UTM or parameters), and the cookie in that browser is linked to the contact.
- Registration. After account creation, the site sends data to the system, and the current session is attached to the new contact.
- Login. At each login, the system receives an event with user data and links the current behavior to the contact.
- Purchase. Order data and contact details are passed together, which also enables matching.
In each of these scenarios, only the browser or device where the action occurred gets stitched. Other devices remain anonymous until the user identifies themselves there as well.
The contact has just appeared in the system, but it already has an accumulated behavioral history. That's why a trigger can fire within the first few minutes — not as a welcome message, but as a continuation of an intent that had already formed.
This scenario is typical. But users rarely leave their contact details on the first visit. In most cases, several sessions pass between the first site visit and identification. That's the window where intent takes shape: users compare products, return to them, and assess the price.
In practice, web tracking makes it possible to:
- shorten the time to first purchase,
- monetize traffic that didn't convert during the first visit,
- close the gap between the first touchpoint and payment,
- personalize the experience from the very first communication,
- keep accumulating data even during unauthenticated sessions.
How to track buyer actions on the site and respond with automated communications?
The same applies to devices. A user might browse a product on mobile and leave their email on desktop. If those actions aren't linked through a contact identifier, part of the intent never reaches the triggers.
As a result, the first communication ends up generic rather than personalized — exactly when it could have closed the sale.
In Yespo CDP, web tracking automatically stores anonymous behavior via cookies, and links it to the user's profile once a contactID is received. In mobile apps, contactID replaces cookies. Even an anonymous user has a separate profile, which — after authorization — is merged with the main contact along with the full event history.
But even within a single device, the effect already measures in tens of percentage points of revenue. With proper cross-device history stitching, that effect scales even further.
How This Works in Practice — the PUMA Case Study
PUMA is a globally recognized sportswear and casual apparel brand with over 75 years of history. The company combines offline retail with ecommerce development and invests in personalizing the customer experience. In 2022, PUMA chose Yespo CDP as a partner for personalized communications and retention strategies. Together with the platform, the team quickly brings new ideas to life — from basic segmentation and trigger scenarios to product recommendations and promo emails with gamified mechanics.
Let's look at a real scenario for one contact at PUMA.
A user was browsing products on the site — sports socks. They left, but eventually returned via a direct visit. They had already viewed products before — the system had recorded this at the anonymous profile level. During the return visit, they were drawn in by a discount offer and left their email in a subscription pop-up in the site footer.
At that moment, the contact was passed to the system via API. But in the system, this was not an empty new subscriber. The history of previous browsing sessions was automatically attached to them.
The contact screen shows that approximately 20 minutes passed between the moment the contact appeared in the system (and registration was confirmed) and the sending of the "Abandoned Browse" email. In other words, the system didn't send a welcome email first — it responded to real intent.
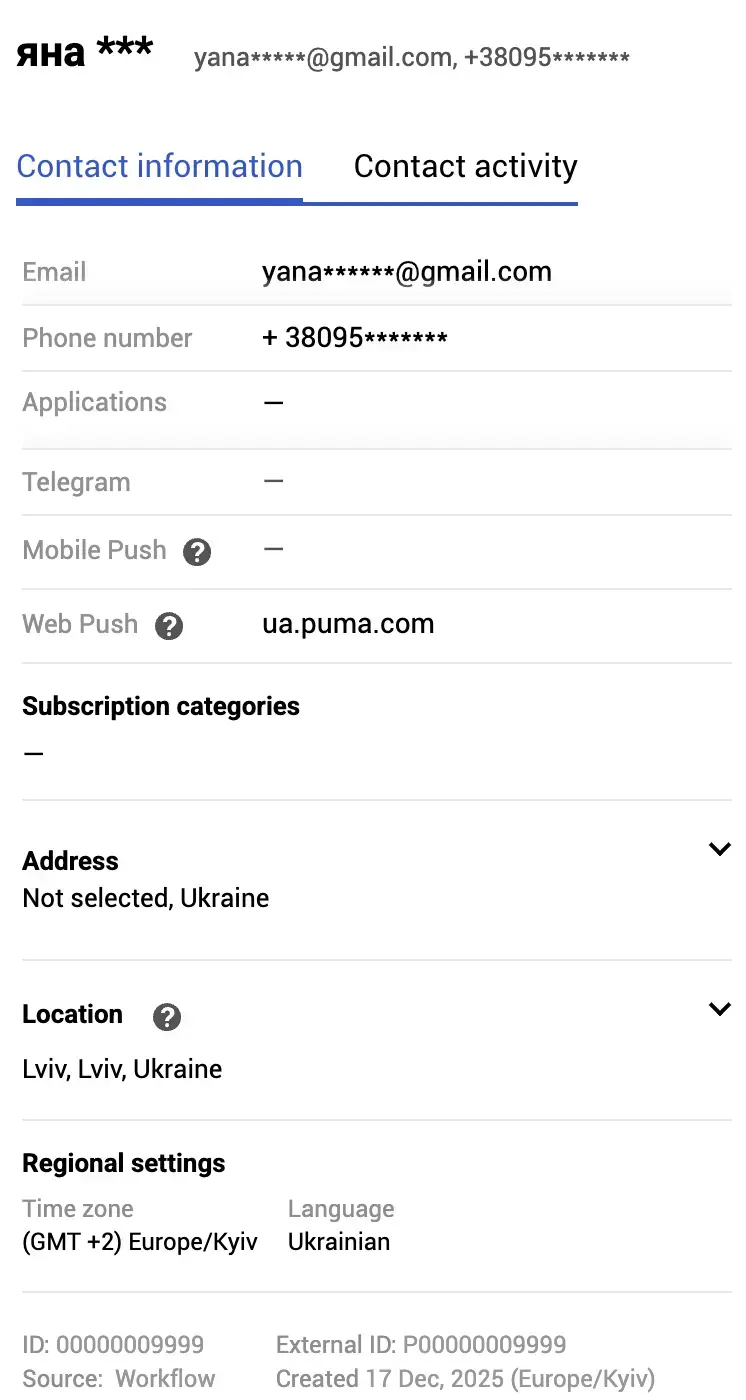
The user received an email containing the specific products they had viewed earlier, along with a personalized AI-driven recommendation selection. The email doesn't begin a new relationship — it picks up right where the user left off.
![[Email with a personalized selection] [Email with a personalized selection]](https://cdn.yespo.io/photos/shares/Blog/puma2_case/image4.webp)
The purchase happened in under an hour after the contact appeared in the system. On the surface, this looks like a fast conversion from a new subscriber. In reality, it's the monetization of intent that had already formed earlier — while the user was still anonymous.
And this is not an isolated case.
What the Data Showed
To understand the scale of the effect, we analyzed 7 months of the "Abandoned Browse" trigger and split all orders by logic that measures revenue generated in the first hours after a contact is identified.
NEW — orders that:
- occurred within 80 minutes of contact creation, or
- are the contact's first order.
OLD — all repeat orders after the first.
8 minutes
is the operational window in which trigger scenarios most commonly fire after identification (abandoned browse, abandoned cart).
Overall, trigger scenarios generate 1.15% of all site orders. The "Abandoned Browse" trigger is the highest-converting among them and accounts for 0.61% of total site revenue.
NEW Share Within the Trigger
Over the analysis period:
- 54.6% of trigger orders came from NEW contacts
- 23.5% of trigger revenue was generated by NEW contacts
This means nearly a quarter of the trigger's revenue is generated within the first hours after a contact appears in the system. Without anonymous history matching, this revenue simply would not have been generated — because the trigger would have had no data to work with.
At the scale of the full site, this is +0.14% in total revenue, generated exclusively by correctly stitching anonymous behavior to contact data within a single trigger.
And this is just one scenario. The same logic can scale across other triggers, segments, and channels.
Conclusion
Anonymous traffic is often treated as the top of the funnel and underestimated — even though that's exactly where intent forms, and where a portion of revenue is being lost.
In the PUMA case, 23.5% of "Abandoned Browse" trigger revenue is generated in the first hours after a contact appears in the system. That means nearly a quarter of this scenario's revenue is directly tied to stitching anonymous history to contact data. At the scale of the full site, this delivers +0.14% in total revenue — with no additional ad spend, purely through better use of existing traffic.
An anonymous user is already ready to buy. The only question is whether your system can see that. If not, a portion of revenue stays outside your control. And as long as it's invisible, it can't be scaled.
We help businesses identify where potential revenue is being lost — and turn those gaps into growth.